Two Factor Authentication (or 2FA) is an absolute must-have for any software – especially if that software stores personal data that requires extra security. But do you know what 2FA actually is or what it does?
What is Two-Factor Authentication?
2FA is an additional layer of security used to ensure the person trying to gain access to an online account is really who they say they are. The first factor involves the usual login steps of entering a username and password. At this point, the person would normally be granted access to the account if the details they entered are correct, but with 2FA, the user is required to provide further information.
The information required to pass the second factor in the authentication process generally comes from one of the following:
Something you know: a personal identification number (PIN), password, ‘secret question’ answers or a keystroke pattern.
Something you have: a debit or credit card, smartphone or small hardware token.
Something you are: a more advanced category which might include a biometric pattern such as a fingerprint, iris scan or voice print.
If even one of these factors is compromised in the slightest way, the account will not be unlocked. This protects 2FA protected accounts from being accessed by anyone other than the legitimate account holder in the event that a password is stolen or a phone or bank card is lost. Websites and apps that use 2FA correctly also allow software providers to be more confident of the user’s identity before unlocking the account.
If you’re using a website or app that only requires a username and password to get in and doesn’t offer two-factor authentication, there’s a good chance that you’re data is vulnerable as it will be eventually be hacked.
Why is Two-Factor Authentication Necessary?
So much of our lives are happening on mobile devices and laptops now, which leaves us and our digital accounts wide open to the mercy of cyber criminals. Malicious attacks against governments, companies and individuals are becoming more and more common, with there being no signs that hacks, data breaches and other forms of cybercrime is slowing down. It’s for this exact reason that we need to do everything possible to improve online security.
There has been a massive increase in the number of websites that have had their users’ data compromised recently; and as cybercrime becomes more sophisticated, companies are finding that their outdated security systems just don’t cut it against these modern threats and attacks.
A lot of the time, it chalks down to simple human error leaving websites and apps exposed to this kind of danger – and it’s not just user trust that can be damaged. All types of organisations – global companies, small businesses, start-ups, and even non-profits – suffer severe financial and reputational loss.
For consumers, the after-effects of targeted hack or identity theft can be devastating. Stolen credentials are used to secure fake credit cards and fund shopping sprees, which can damage a victim’s credit rating. And entire bank and cryptocurrency accounts can be drained overnight. In fact, police statistics have revealed that a whopping £190,000 is lost by UK victims of cybercrime every day. That’s over £300 million per year!
Why are Passwords Unreliable?
This raises one question that is on everyone’s mind – how did passwords become so vulnerable?
Usernames and passwords have always been (and remain to this day) the most common form of user authentication. The general rule of thumb is that a password should be something only you know while being difficult for anyone else to guess – usually comprising a combination of upper and lower case letters, numbers and special characters.
While using passwords is better than having no protection at all, they’re not foolproof by any stretch of the imagination.
People have terrible memories: A recent report looked at over 1.4 billion stolen passwords and found that most were embarrassingly simple. Among the worst are common words and sequences such as ‘111111’, ‘123456’, ‘qwerty’ and “password’. All very easy to remember, but any half-baked hacker could crack these simple passwords in next to no time at all.
Too many accounts: As users get more comfortable with doing everything online, they open more and more accounts. This eventually creates too many passwords to remember and paves the way for a dangerous habit: password recycling. Hackers love this trend because it takes just seconds for hacking software to test thousands of stolen sign-in credentials against popular online banks and shopping sites. If a username and password pair is recycled, it’s extremely likely it’ll unlock plenty of other lucrative accounts.
Security fatigue sets in: To protect themselves, some consumers try to make it harder for attackers by creating more complex passwords. But many just give up and fall back to using weak passwords across multiple accounts.
Luckily, it’s easy for businesses to add an extra level of protection to user accounts in the form of two-factor authentication.
Common Types of Two-Factor Authentication
There are several types of two-factor authentication in use today; some may be stronger or more complex than others, but all offer better protection than passwords alone. Let’s look at the most common forms of 2FA.
Hardware Tokens for Two-Factor Authentication
Hardware tokens, possibly the oldest form of 2FA, are small keyfob-like devices that produce a new numeric code every 30-seconds. When a user tries to access an account, they are required to enter the code displayed on the device’s screen into the site or app. Some versions of hardware tokens automatically transfer the 2FA code when plugged into a computer’s USB port. These hardware tokens are most commonly used by banks to help their customers log into online and mobile banking more securely.
SMS Text-Message and Voice-based 2FA
SMS-based 2FA interacts directly with a user’s phone. After a username and password are entered to a site, it sends the user a unique one-time passcode (OTP) via text message. As with the hardware token process, the user is then required to enter the OTP back into the application before getting access. Similarly, voice-based 2FA automatically dials a user and verbally delivers the 2FA code.
Software Tokens for 2FA
The most popular form of two-factor authentication uses a software-generated, time-based, one-time passcode (also called TOTP, or ‘soft-token’). This method requires users to download and install a free 2FA app on their smartphone or desktop. They can then use the app with any site that supports this type of authentication. Like with other 2FA options, a username and password needs to be entered first. When prompted, the user then has to enter the code shown on the app. Similar to hardware tokens, the soft-token is typically valid for less than a minute, and because the code is generated and displayed on the same device, soft-tokens remove the chance of hacker interception.
Push Notification for 2FA
Websites and apps can send a user push notifications when authentication is being attempted. If it’s the user attempting to log in, they can simply approve access via the notification to get into their account. Otherwise, they can deny access with a single touch and flag up to the service provider that someone other than themselves attempted to log into the account. The push notification method is passwordless, with no codes to enter and no additional interaction required.
Push notifications eliminate any opportunity for phishing, man-in-the-middle attacks, or unauthorised access by providing a direct and secure connection between the service provider, 2FA service and the device.
Other Forms of Two-Factor Authentication
These are the four most common types of 2FA, but the list isn’t extensive. Recent innovations include verifying a person’s identity via fingerprints, retina patterns, and facial recognition. Ambient noise, pulse, typing patterns, and vocal prints are also being explored.
Staff Squared uses Two-Factor Authentication!
According to a recent report, stolen, reused and weak passwords remain a leading cause of security breaches. Unfortunately, passwords are still the main (or only) way many companies protect their users.
The good news is that cybercrime is being talked about so much that 2FA awareness is quickly growing and users are demanding that the companies they do business with have improved security – and we couldn’t agree more! In fact, we believe that any software providers that don’t offer 2FA to their customers are neglecting the responsibility to protect their data.
Here at Staff Squared, we take the security of our customers’ data and the confidence that they have in us to protect their personal information very seriously. We are proud to offer 2FA, which gives Staff Squared users the trust they need and want in their HR solution.
Users now have the option to enable 2FA in their accounts, giving them more confidence than ever that their personal data is as safe as can be while it lives in Staff Squared. Setting this up couldn’t be more straightforward, either!
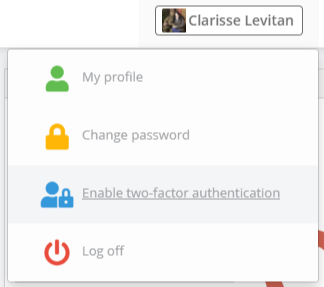
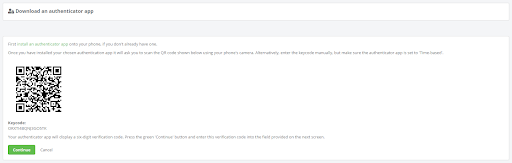
By simply selecting the option to ‘enable two-factor authentication’ in the dropdown menu shown below, users will be taken to a screen where they will be asked to scan a QR code.
If they don’t already have an authenticator app on their phone, it couldn’t be easier to install one. There are plenty of apps out there which can be downloaded to any iOS or Android device. Google Authenticator is a great one. Once users have scanned the code on their screen and clicked ‘continue’, they will be asked to enter a six-digit authentication code which will appear on their screens.
As soon as this code is entered, users will be asked to retrieve an authentication code each time they attempt to log in – alternatively, they can select the ‘remember me’ option at the point of login to bypass this step for 30 days on the computer they are logging into.
For more information on 2FA or if you would like assistance in getting this set up, please do not hesitate to contact a member of our customer care team on 0800 033 7569 or at [email protected].